-

Cyber Threats Part 4: Ransomware Attacks
The fourth in a five-part cyber threat series focuses on ransomware attacks where information or computer networks are held hostage…
-

Protecting Yourself From Mass Public Shootings
Most of the material I have produced on personal security, such as articles discussing how to practice situational awareness, counter…
-
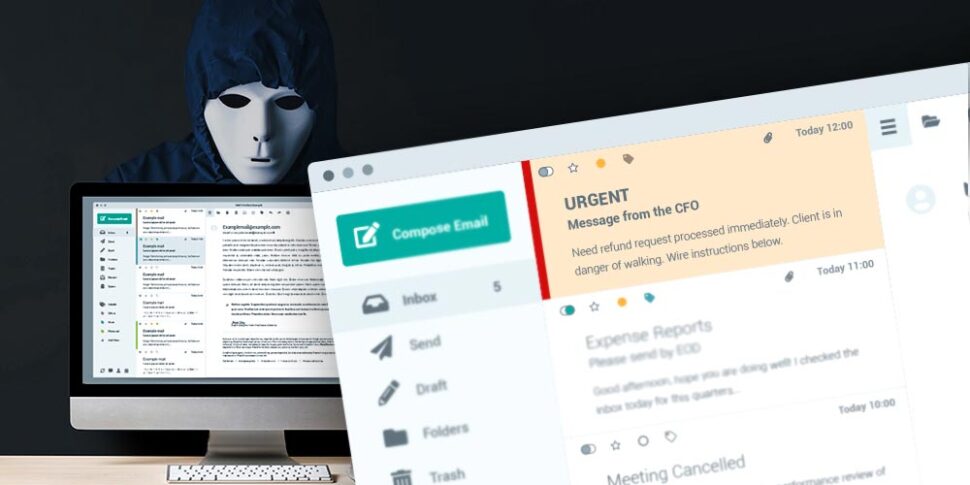
Cyber Threats Part 3: Business Email Compromise
The third in a five-part series demystifies business email compromise schemes and how they target those who transfer funds electronically.…
-

Cyber Threats Part 2: Phishing and Spear Phishing Attacks
The second in a five-part series explores phishing, and the more targeted spear phishing attack, and how they manipulate information…
-
Cyber Threats Part 1: Understanding the Cyber Attack Cycle
Cyber attacks leverage information to gain access to proprietary networks, electronic devices, and chains of command in order to gain…
-

Cyber Security and Human Vulnerability
Keeping a company safe from cyber attacks often only includes technical security such as properly installed hardware with up-to-date firmware,…
-

Propaganda of the Deed: Contextualizing the Buffalo Attack
The shooting in Buffalo, NY exemplifies how white supremacists use the internet to broadcast their attacks to spotlight their radicalized…
-

Placing Bomb Threats in Perspective
In the wake of the recent wave of bomb threats placed to Historically Black Colleges and Universities (HBCUs) I have…
-
Organizational Contingency Plans: Defined, Fluid, Crucial
The threat of a potential Russian invasion of Ukraine has pushed to the forefront discussions regarding contingency plans, trip wires,…
-

The Need for Nuance in Protective Intelligence Part 4: Extinction Rebellion
Since its inception in the UK in October of 2018, XR has become one of the fastest-growing protest campaigns in…
CALL US: (877) 897-6428
