
Cyber Threats Part 5: Supply Chain Attacks
By TorchStone Senior Analyst, Ben West
Supply chain attacks are an indirect approach to breaching a target’s defenses by compromising a vendor or partner of the organization and exploiting trusted connections to gain access to proprietary networks.
While Supply Chain attacks may not be as common as some of the other threats this series has addressed so far, the frequency of attacks is increasing.
Accenture noted in its 2021 The State of Cybersecurity Resilience report that the rate of successful breaches via victims’ supply chains increased from 44% in 2020 to 61%.
The primary advantage of a Supply Chain attack is its ability to grant access to thousands of targets via one well-placed attack.
SolarWinds
One of the most damaging cyber-attacks in years, the 2020 SolarWinds attack, exploited supply chains to compromise thousands of victim organizations in the private and public sectors.
The appeal of SolarWinds’ software-as-a-service is that the company could push out updates, improvements, and security patches automatically to its clients, ensuring that they always had the latest version of the software.
Around September of 2019, suspected Russian hackers targeted and breached the software company.
Rather than raiding SolarWinds of IP and/or cash flows as demonstrated in previous cyberattack methods, the group behind the attack, Nobelium, used its access to SolarWinds to gain access to its clients.
In 2020, upwards of 30,000 private and public organizations relied on SolarWinds’ Orion software management services to run their IT.
Nobelium exploited this convenience by injecting malicious code into the software updates that were distributed through legitimate, trusted updates from SolarWinds.
Well over half of SolarWinds’ clients (18,000) downloaded the corrupted updates, essentially granting the hackers access to their networks.
The most heavily targeted organizations appear to have been government agencies such as Homeland Security, State, Commerce, and Treasury, where hackers likely had access to sensitive information and passed it on to handlers in the Russian government.
The attack was not discovered until the end of 2020, meaning that the attackers had an astounding 14 months to carry out their attack.
The 2020 SolarWinds attack was certainly not the first of its kind.
M.E.Doc
In 2017, Russian-backed hackers distributed their NotPetya attack via a Ukrainian accounting software firm that had up to 400,000 subscribers at the time, including components of major corporations like logistics company DHL, shipping giant Maersk, and food manufacturer Mondelez International.
Similar to SolarWinds, the attackers first gained access to the relatively small (and poorly secured) Ukrainian company that distributed and supported the accounting software M.E.Doc.
Rather than attacking the company directly, the hackers elevated their access by distributing malware via M.E.Doc’s automatic updates.
This expanded the scope of the attack from one little-known Ukrainian software firm to some of the biggest companies in the world.
While the exact purpose of the attack remains unclear, the damage associated with it was enormous, costing an estimated $10 billion in losses due to system downtime and investments in new equipment to cover losses.
Some researchers suggested that Russia had no other motive than disruption, demonstrating its ability to wreak havoc on the global economy through cyberattacks.
It is important to note here that in both the SolarWinds and NotPetya attacks outlined above, companies were following best practices by allowing software providers to push out updates and patches to their clients.
The ability to automatically patch software vulnerabilities is a major cyber security advantage that prevents clients from falling prey to already known and circulating exploits.
Like an auto-immune disease that turns a human body against itself, Supply Chain attacks are especially nefarious in that they attack and undermine the very process that helps vendors keep their clients safe from more routine cyber attacks.
Airbus
Chinese cyber threat actors have also demonstrated their interest in supply chain attacks, as demonstrated by a series of probes and breaches into vendors and suppliers connected to European aerospace company Airbus—a longtime Chinese industrial espionage target.
China had long demonstrated interest in Airbus’ intellectual property as it sought to support its own state-backed aerospace company, Comac, and the company’s efforts to manufacture and sell its own commercial jetliner.
In 2017 and 2018, Chinese hackers were successful at breaching Airbus through a series of supply chain attacks via suppliers like Rolls-Royce and consultant Expleo.
Altogether, hackers targeted at least four Airbus vendors and partners in their effort to reach their target.
The Airbus attack demonstrates how Supply Chain attacks can target specific companies in addition to maximizing the target set, as also revealed in the SolarWinds and NotPetya attacks.
The attack also reinforces the rule of thumb that an organization’s cyber security is only as good as its weakest link—and those links extend to external partners not directly under the control of the primary target’s IT security department.
Securing Links
Regardless of how much an organization has invested in its own cyber security, if it is allowing outside vendors access to its networks, the organization is vulnerable to attack.
One instinctual response to the threat of supply chain attacks could be to turn off software updates and deny vendors access to proprietary networks in the first place.
But this makes an organization more vulnerable to attack by running unpatched software—or putting more burden on an IT security department that has to track everything itself.
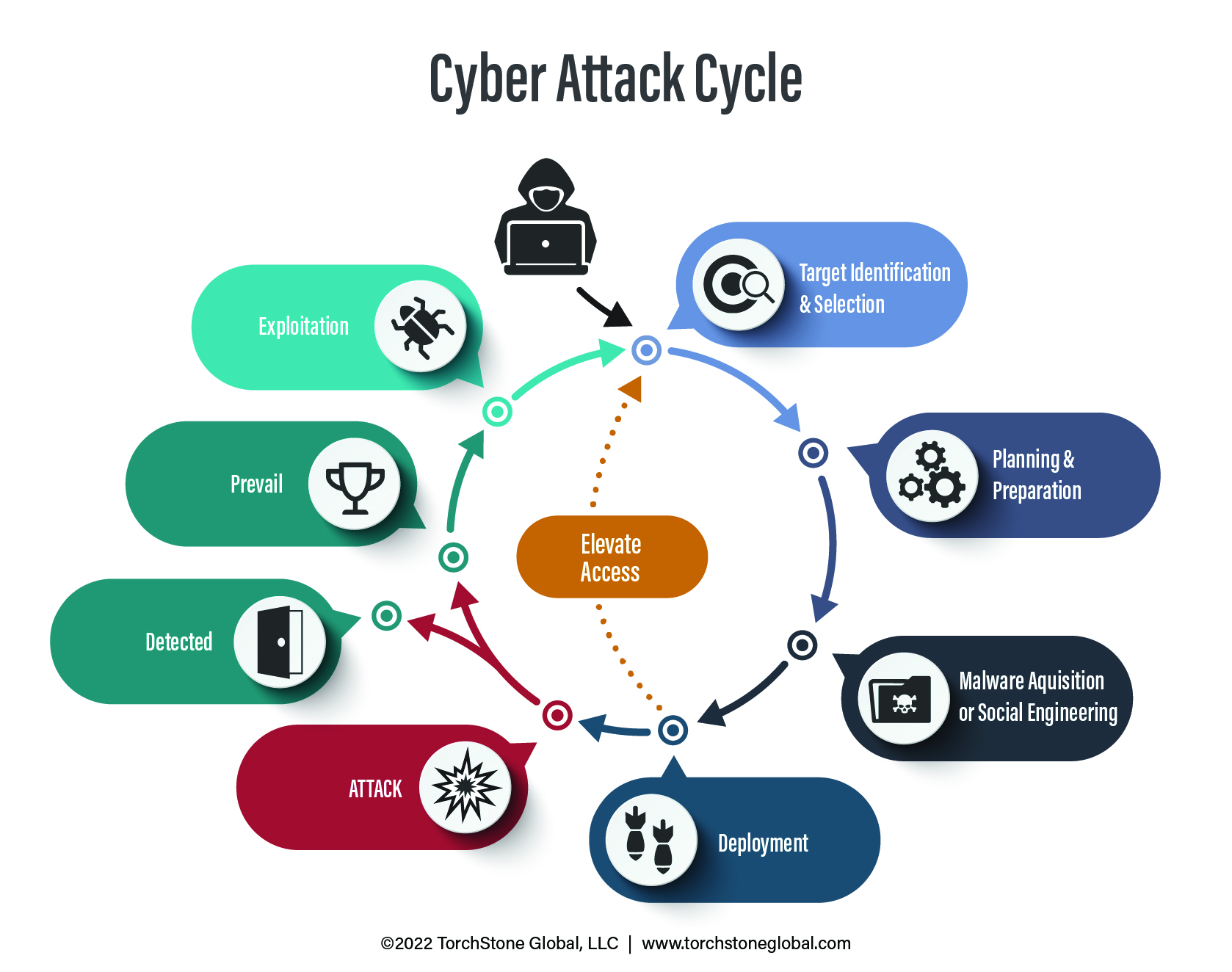
However, understanding the Cyber Attack Cycle and how it can be interrupted can lead to a better response to the threat of Supply Chain attacks.
Organizations must ensure that vendors and partners that have network access are reliable and doing their part to keep their own networks secure.
Just like corporate security departments would vet any new hire coming into the company, they should also vet any new vendor or partner that gains access to the organization’s network.
Vetting should be followed up with regular audits over the duration of the relationship to ensure that the partner company is continuing to invest in cyber security and staying up-to-date on the latest threats.
With the rise in Supply Chain attacks and the potential for extensive damage should one occur, vendors and partners should be open to such requests.
This report is the fifth in a five-part series addressing cyber threats to organizations and individuals. The first part of the series, Understanding the Cyber Attack Cycle, introduces the Cyber Attack Cycle and its progression. The second part, Phishing and Spear Phishing Attacks, demystifies the most common cyber security threat. The third part, Business Email Compromise, illustrates how information received from a spear phishing attack may be used. The fourth part of the series, Ransomware Attacks, discusses how information or network access may be held hostage.
